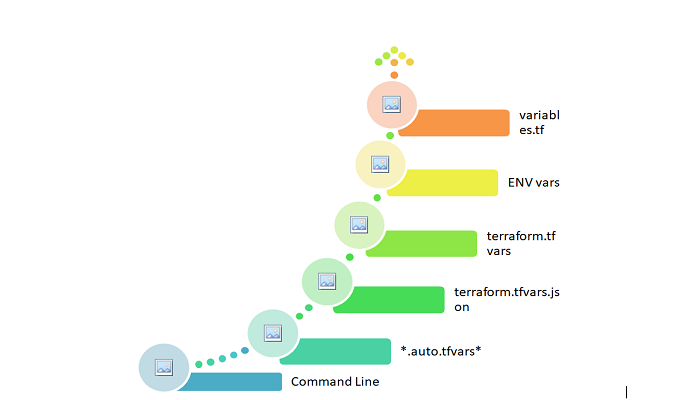
This post is about Terraform’s Variable
If you’re unfamiliar with Terraform and its applications, start here for an overview.
Terraform’s Variable
The customer receives a response as soon as he opens the URL. The request then uses a mapping of IP addresses from DNS records to identify its destination, landing on a server that owns this IP, and the server processes to give a response, which is then transmitted back to the request’s origin. Because we’re using Amazon Web Services (AWS), we’ll use an EC2 instance. In production, simply having an EC2 instance that can process requests is insufficient. Virtual private cloud plays an important role to separate networks and other virtual networks from the cloud(AWS).
An EC2 instance can be run in the virtual network; is created with the help of AWS service as VPC. Unlike data center networks, switches, and routers, VPC is a software-defined network intended for packet transfers throughout AWS regions. AWS VPC is secure as it provides various features to protect the cloud.
A CIDR block, such as 10.0.0.0/16, must be specified when creating a VPC. A CIDR block is a collection of Internet Protocol standards being used to provide unique identities for networking and devices. As soon as a VPC is created, one or more subnets can be added to each availability zone. Each subnet’s CIDR block is a part of the VPC CIDR block. We seek an internet gateway that allows us to communicate over the internet.
The internet gateway functions as a router, receiving packets from our EC2 instance and sending them out into the open network. With the help of a routing table, traffic flows to an internet gateway from a public subnet. All instances on a public subnet, with the help of IG, are connected to the internet. To allow our instance to broadcast traffic to the internet, we’ll use a public subnet.
VPC is securely created with the default inbound rules. We’ll need to build a security group that works as a virtual firewall for our EC2 instance’s traffic. Ingress and egress regulations are set by us. Ports, the port utilized for access from the port, and the destination port to port must all be accepted in the rules. To send or receive traffic to and from our EC2 instance, we must connect this security group with it.
In this scenario, we’ll implement an ingress rule to allow inbound traffic on port 22 then we can SSH into our instance, as well as an egress rule to allow all content to reach the public internet. To enter into the instance via SSH, we must first create a key pair, link it to the EC2 instance, and connect using the private key. The public key is for Amazon EC2, and the private key is for us which is used to connect SSH. Terraform will be used to produce all of these resources. Within the VPC, there is a subnet.
Let’s make a list of all the resources that need to be created in order to run an EC2 instance inside a virtual private network, as this will help us understand better.
- VPC
- VPC’s subnet
- VPC has an associated Internet gateway.
- The route, which is a part of VPC, directs the traffic to IG.
- To make our subnet a public subnet, we need to associate a routing table with it.
- VPC’s security group.
- For SSH access, a key pair is used.
- Within our public subnet, we have an EC2 instance with a security group and a generated key pair.
We may try to designate some of our inputs as variables so that they can be readily modified and maintained now that we have a clear image of what resources we need to provide for our production setup with EC2.
- VPC >> CIDR block.
- VPC >> CIDR block >> Subnet CIDR block.
- Availability zone.
- The path to the public key is used to create key pairs.
- AMI would be used to establish an EC2 instance.
- EC2 instance type.
- With AWS, we can begin tagging our resources to keep track of them. We’re going to use the environment tag.
Please see this post Terraform Variable with Example for a practical example.
/////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
Keep Reading About Terraform
That’s all for Terraform’s Variable



