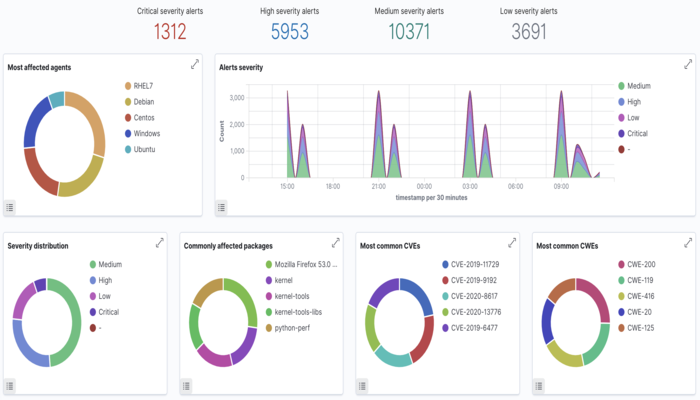
This post is about Wazuh Vulnerability detection
Prerequisites
Install wazuh Open Source security platform and wazuh agent by using below mentioned blogs.
1:WAZUH The Open Source Security Platform
Wazuh is able to detect vulnerabilities in the applications installed in agents using the Vulnerability Detector module. This software audit is performed through the integration of vulnerability feeds indexed by Canonical, Debian, Red Hat, and the National Vulnerability Database.
How it works
To be able to detect vulnerabilities, now agents are able to natively collect a list of installed applications, sending it periodically to the manager (where it is stored in local sqlite databases, one per agent). Also, the manager builds a global vulnerability database, from publicly available CVE repositories, using it later to cross-correlate this information with the agent’s applications inventory data.
The global vulnerability database is created automatically, currently pulling data from the following repositories:
- https://canonical.com: Used to pull CVEs for Ubuntu Linux distributions.
- https://www.redhat.com: Used to pull CVEs for Red Hat and CentOS Linux distributions.
- https://www.debian.org: Used to pull CVEs for Debian Linux distributions.
- https://nvd.nist.gov/: Used to pull CVEs from the National Vulnerability Database.
- https://feed.wazuh.com/: Used to pull the MSU feed with CVEs and patches for Microsoft products.
This database can be configured to be updated periodically, ensuring that the solution will check for the very latest CVEs.
Once the global vulnerability database (with the CVEs) is created, the detection process looks for vulnerable packages in the inventory databases (unique per agent). Alerts are generated when a CVE (Common Vulnerabilities and Exposures) affects a package that is known to be installed in one of the monitored servers. A package is labeled as vulnerable when its version is contained within the affected range of a CVE. The results are presented as alerts and also stored in a database. So you can check the last scan alerts, or query every single agent’s vulnerable software DB.
Scan types
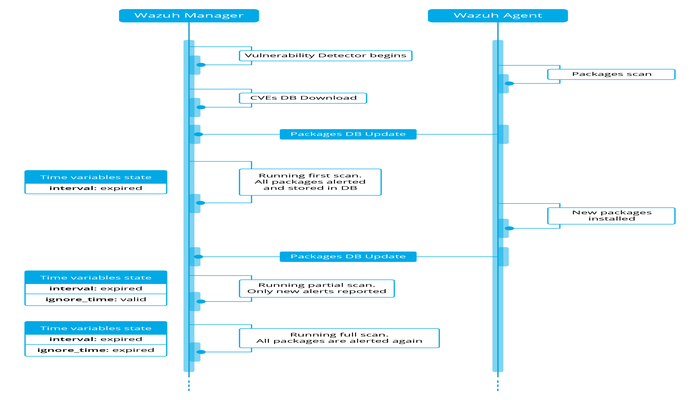
The Vulnerability Detector module can run a scan on startup (run_on_start) and every certain period of time (interval). In any of these cases, the packages that have already been scanned will wait until the ignore_time expires to be re-scanned. This improves the performance and avoids repeated alerts during a configurable time. We have then two different types of scan:
- Full scan: The first time, Vulnerability Detector scans every single package installed. After this, all the available packages are scanned again only when the configured ignore_time expires.
- Partial scans: Only new packages are scanned while ignore_time is still valid.
There are few considerations that arise from this behavior:
- Every full scan generates alerts for all the packages, so the alerts are repeated until they get fixed.
- The user cannot trigger a full scan manually, the only option is to decrease the ignore_time setting.
- The partial scans generate alerts for new packages, but they do not delete alerts for removed packages.
- Partial scans can be triggered with a Manager restart.
Check Vulnerability detector settings for more configuration details.
The following example may be useful to understand all steps involved
Compatibility matrix
The following table shows the operating systems where the vulnerability detector currently is supported and the provider configuration needed for each distribution.
| Distribution | Versions | Configuration provider |
|---|---|---|
| Red Hat & CentOS | 5 | Red HatNational Vulnerability Database |
| 6 | ||
| 7 | ||
| 8 | ||
| Ubuntu | trusty / 14 | CanonicalNational Vulnerability Database |
| xenial / 16 | ||
| bionic / 18 | ||
| focal / 20 | ||
| Debian | stretch / 9 | DebianNational Vulnerability Database |
| buster / 10 | ||
| Windows | All supported versions | National Vulnerability DatabaseMSU |
| MacOS | All supported versions | National Vulnerability Database |
Vulnerability detection
The following example shows how to configure the necessary components to run the vulnerability detection process.
- Enable the agent module used to collect installed packages on the monitored system.
It can be done by adding the following block of settings to your shared agent configuration file:
<wodle name="syscollector">
<disabled>no</disabled>
<interval>1h</interval>
<os>yes</os>
<packages>yes</packages>
</wodle>If you want to scan vulnerabilities in Windows agents, you will also have to add the hotfixes scan:
<wodle name="syscollector">
<disabled>no</disabled>
<interval>1h</interval>
<os>yes</os>
<packages>yes</packages>
<hotfixes>yes</hotfixes>
</wodle>These scans are enabled by default. For more information about the inventory module, check Syscollector settings.Enable the manager module used to detect vulnerabilities.
You can do this adding a block like the following to your manager configuration file:
<vulnerability-detector>
<enabled>yes</enabled>
<interval>5m</interval>
<run_on_start>yes</run_on_start>
<provider name="canonical">
<enabled>yes</enabled>
<os>bionic</os>
<update_interval>1h</update_interval>
</provider>
<provider name="nvd">
<enabled>yes</enabled>
<update_from_year>2010</update_from_year>
<update_interval>1h</update_interval>
</provider>
</vulnerability-detector>Remember to restart the manager to apply the changes:
systemctl restart wazuh-manager
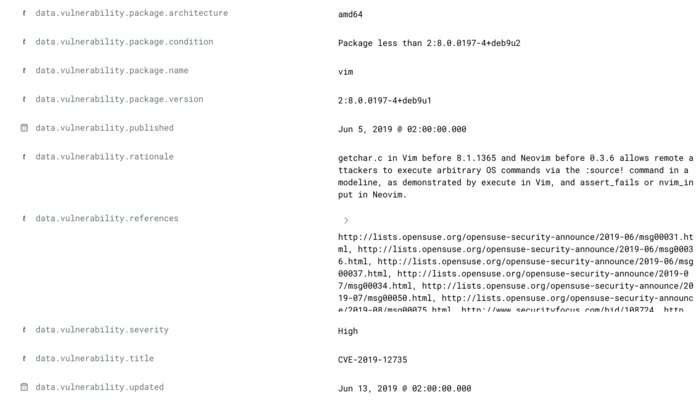
service wazuh-manager restartHere, you can see a real alert where the explained fields are filled:
** Alert 1591945867.49829472: - vulnerability-detector,gdpr_IV_35.7.d,pci_dss_11.2.1,pci_dss_11.2.3,tsc_CC7.1,tsc_CC7.2,
2020 Jun 12 07:11:07 (Debian) any->vulnerability-detector
Rule: 23505 (level 10) -> 'CVE-2019-12735 affects vim'
vulnerability.package.name: vim
vulnerability.package.version: 2:8.0.0197-4+deb9u1
vulnerability.package.architecture: amd64
vulnerability.package.condition: Package less than 2:8.0.0197-4+deb9u2
vulnerability.cvss.cvss2.vector.attack_vector: network
vulnerability.cvss.cvss2.vector.access_complexity: medium
vulnerability.cvss.cvss2.vector.authentication: none
vulnerability.cvss.cvss2.vector.confidentiality_impact: complete
vulnerability.cvss.cvss2.vector.integrity_impact: complete
vulnerability.cvss.cvss2.vector.availability: complete
vulnerability.cvss.cvss2.base_score: 9.300000
vulnerability.cvss.cvss3.vector.attack_vector: local
vulnerability.cvss.cvss3.vector.access_complexity: low
vulnerability.cvss.cvss3.vector.privileges_required: none
vulnerability.cvss.cvss3.vector.user_interaction: required
vulnerability.cvss.cvss3.vector.scope: changed
vulnerability.cvss.cvss3.vector.confidentiality_impact: high
vulnerability.cvss.cvss3.vector.integrity_impact: high
vulnerability.cvss.cvss3.vector.availability: high
vulnerability.cvss.cvss3.base_score: 8.600000
vulnerability.cve: CVE-2019-12735
vulnerability.title: CVE-2019-12735
vulnerability.rationale: getchar.c in Vim before 8.1.1365 and Neovim before 0.3.6 allows remote attackers to execute arbitrary OS commands via the :source! command in a modeline, as demonstrated by execute in Vim, and assert_fails or nvim_input in Neovim.
vulnerability.severity: High
vulnerability.published: 2019-06-05
vulnerability.updated: 2019-06-13
vulnerability.cwe_reference: CWE-78
vulnerability.references: ["http://lists.opensuse.org/opensuse-security-announce/2019-06/msg00031.html", "http://lists.opensuse.org/opensuse-security-announce/2019-06/msg00036.html", "http://lists.opensuse.org/opensuse-security-announce/2019-06/msg00037.html", "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00034.html", "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00050.html", "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00075.html", "http://www.securityfocus.com/bid/108724", "https://access.redhat.com/errata/RHSA-2019:1619", "https://access.redhat.com/errata/RHSA-2019:1774", "https://access.redhat.com/errata/RHSA-2019:1793", "https://access.redhat.com/errata/RHSA-2019:1947", "https://bugs.debian.org/930020", "https://bugs.debian.org/930024", "https://github.com/neovim/neovim/pull/10082", "https://github.com/numirias/security/blob/master/doc/2019-06-04_ace-vim-neovim.md", "https://github.com/vim/vim/commit/53575521406739cf20bbe4e384d88e7dca11f040", "https://lists.debian.org/debian-lts-announce/2019/08/msg00003.html", "https://lists.fedoraproject.org/archives/list/[email protected]/message/2BMDSHTF754TITC6AQJPCS5IRIDMMIM7/", "https://lists.fedoraproject.org/archives/list/[email protected]/message/TRIRBC2YRGKPAWVRMZS4SZTGGCVRVZPR/", "https://seclists.org/bugtraq/2019/Jul/39", "https://seclists.org/bugtraq/2019/Jun/33", "https://security.gentoo.org/glsa/202003-04", "https://support.f5.com/csp/article/K93144355", "https://support.f5.com/csp/article/K93144355?utm_source=f5support&utm_medium=RSS", "https://usn.ubuntu.com/4016-1/", "https://usn.ubuntu.com/4016-2/", "https://www.debian.org/security/2019/dsa-4467", "https://www.debian.org/security/2019/dsa-4487", "https://nvd.nist.gov/vuln/detail/CVE-2019-12735", "https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12735"]
vulnerability.assigner: [email protected]
vulnerability.cve_version: 4.0Finally, here you can see how the highlighted fields of the alert look in the WUI: