FTP or File Transfer Protocol, is a popular protocol for transferring files to and from an FTP server. However, it is fraught with security risks since it sends data and sensitive information in plain text. VSFTPD ( Very Secure FTP Daemon ) is a fast, secure and stable FTP server that uses encryption to secure data exchanged with the server.
In this tutorial, we’ll install vsftpd FTP server on Debian 11.
Step 1: Install vsftpd package
Firstly, update the package list and upgrade your Debian server.
# apt update
# apt upgrade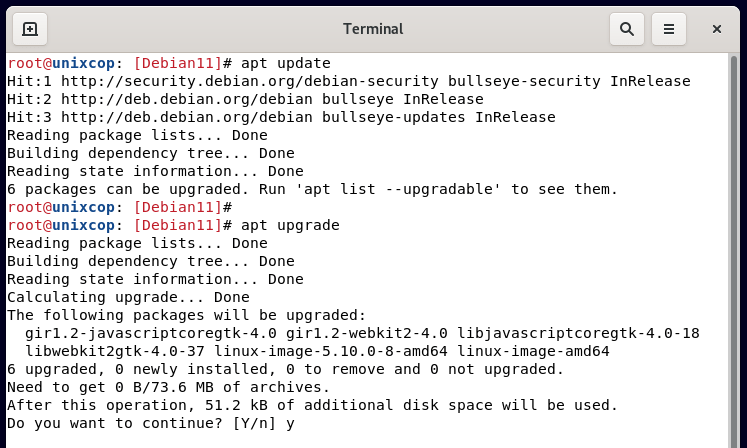
Then install The vsftpd package.
# apt install vsftpd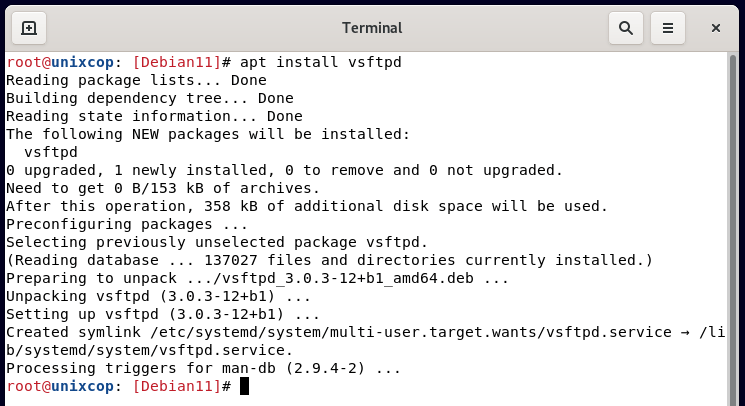
Once installed, vsftpd starts automatically. You can confirm this by running the command:
# systemctl status vsftpd.service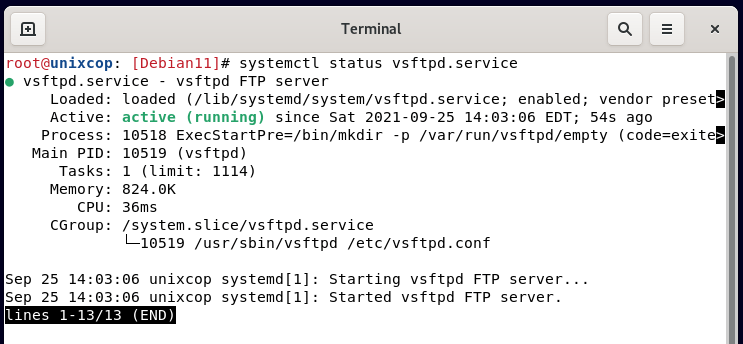
Step 2: Create a FTP user
Next, we are going to create a unique FTP user account that we are going to use to log in to the FTP server. use the adduser command followed by the name of the user and respond to the prompts accordingly.
# adduser unixcop-user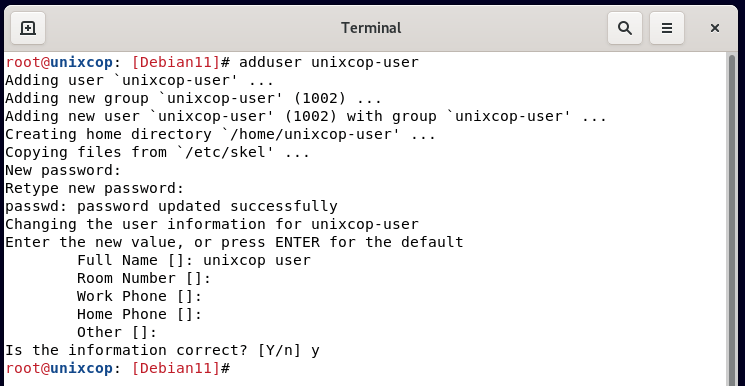
Step 3: Add FTP user to the list of allowed login users
Now, we will add the FTP user to the vsftp.userlist file. Local users specified in this file are granted permission to access the FTP server.
# echo unixcop-user >> /etc/vsftpd.userlist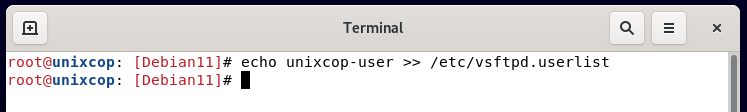
Step 4: Create FTP user directory
Now, create an FTP directory for the FTP user and assign the appropriate directory permissions and ownership.
# mkdir -p /home/unixcop-user/ftp-dir
# chmod -R 750 /home/unixcop-user/ftp-dir
# chown -R unixcop-user: /home/unixcop-user/ftp-dir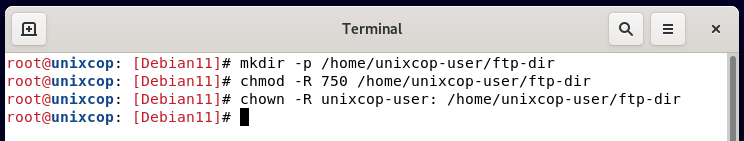
Step 5: Configure vsftpd service
Now we must proceed and edit the main configuration file /etc/vsftpd.conf
# nano /etc/vsftpd.confBy default, anonymous users are granted access. But this is not what we want due to security purposes. Therefore, we will disable login by the anonymous user and only grant access to the local user.
anonymous_enable=NO
local_enable=YESNext, you need to allow the local user to upload files and gain access to their home directory as well as make changes to the files as indicated.
write_enable=YES
chroot_local_user=YES
allow_writeable_chroot=YESAdditionally, you can limit the local users who can access and upload files by specifying only the users contained in the /etc/vsftpd.userlist file.
userlist_enable=YES
userlist_file=/etc/vsftpd.userlist
userlist_deny=NOTo provide a secure FTP connection to the server, we need to encrypt the server using an SSL certificate. We are going to generate a self-signed SSL certificate to encrypt the server. To do so run the command.
# openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/vsftpd-key.pem -out /etc/ssl/private/vsftpd-cert.pem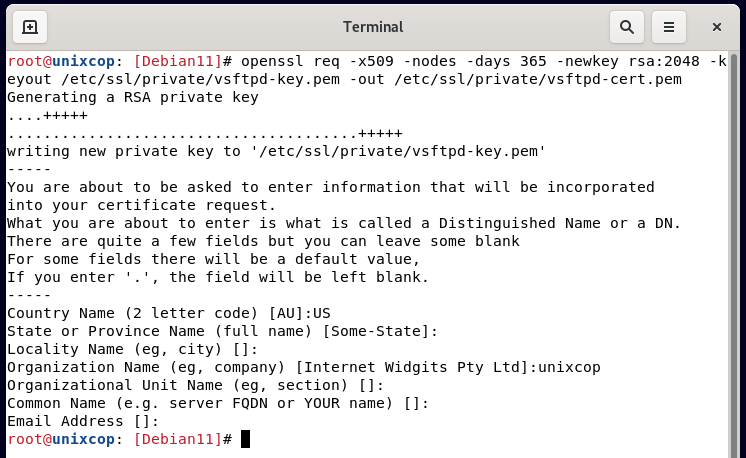
Head back to the default configuration file /etc/vsftpd.conf , and paste these lines to specify the path of the generated SSL certificates and enable SSL.
rsa_cert_file=/etc/ssl/private/vsftpd-cert.pem
rsa_private_key_file=/etc/ssl/private/vsftpd-key.pem
ssl_enable=YESIn summary, your configuration file should contain these lines:
listen=NO
listen_ipv6=YES
anonymous_enable=NO
local_enable=YES
write_enable=YES
dirmessage_enable=YES
use_localtime=YES
xferlog_enable=YES
connect_from_port_20=YES
chroot_local_user=YES
secure_chroot_dir=/var/run/vsftpd/empty
pam_service_name=vsftpd
rsa_cert_file=/etc/ssl/private/vsftpd.pem
rsa_private_key_file=/etc/ssl/private/vsftpd.pem
ssl_enable=YES
user_sub_token=$USER
local_root=/home/$USER/ftp
userlist_enable=YES
userlist_file=/etc/vsftpd.userlist
userlist_deny=NOFor the changes to come into effect, restart the server.
# systemctl restart vsftpd.service
# systemctl status vsftpd.service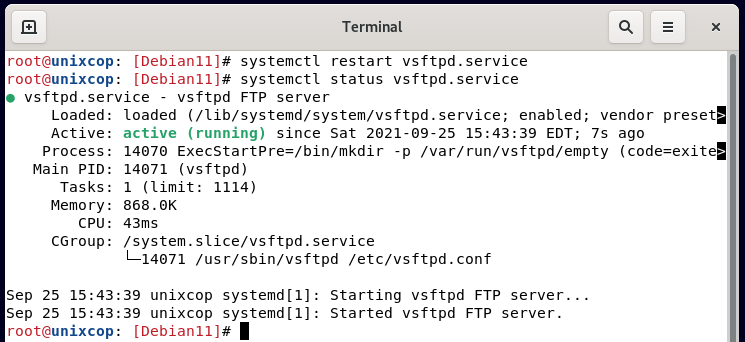
Step 5: Access the vsftpd server
We are now done with the configurations. The last thing is to allow ports 20 and 21 if the firewall is enabled.
# ufw allow 20/tcp
# ufw allow 21/tcp
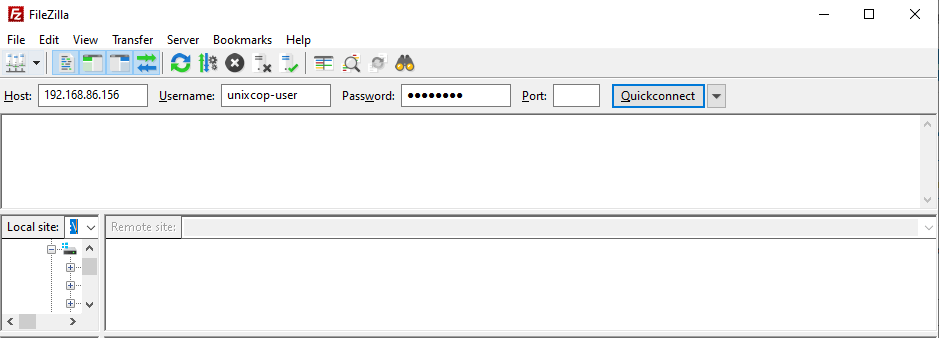
# ufw reloadFinally, grab your FTP client such as FileZilla, and fill in the details as follows:
Host: server-IP
Username: unixcop-user
Password: Password of unixcop-user
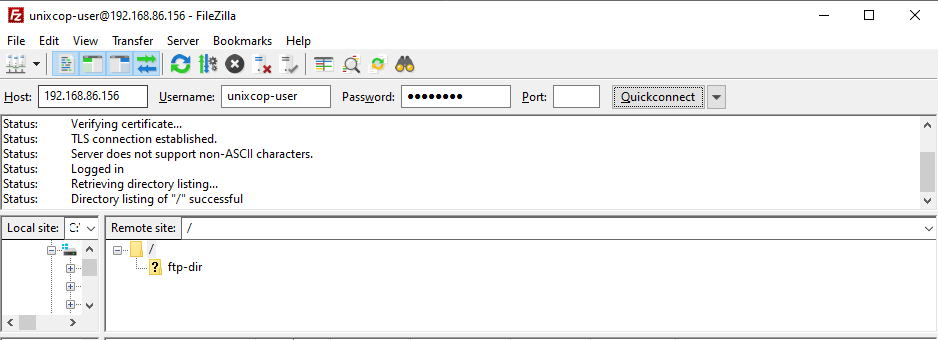
After the successful directory listing, you can now begin transferring files securely over SSL.
And like that, we learned how to install the vsftpd ftp server on Debian 11.




hello, i cant connect the tp server with windows client with the winscp can u help me?
check ur ports and authentication methods