Introduction
CSF is a Stateful Packet Inspection (SPI) firewall, Login/Intrusion Detection and Security application for Linux servers.
t consists of the firewall itself (CSF) which is comprehensive, straightforward, easy, and flexible to configure.
It also has a Login Failure Daemon (LFD) that perfectly complements CSF. This LFD runs all the time and periodically (every X seconds) scans the latest log file entries for login attempts against your server that continually fail within a short period of time. Such attempts are often called “Brute-force attacks” and the daemon process responds very quickly to such patterns and blocks offending IP’s quickly
Install CSF on CentOS 8
As expected CSF is not available in the official CentOS repositories. However, it is possible to install it as it is strongly linked to Perl and this language is supported on CentOS 8.
So, open a terminal session and update CentOS 8
sudo dnf installIn the end, install the Perl elementary modules and other tools that we will use later like vim
sudo dnf install @perl curl tar vimAt the end of the installation, you have to install other extra Perl modules on CentOS 8
sudo dnf install perl-libwww-perl.noarch perl-LWP-Protocol-https.noarch perl-GDGraphYou can verify the installation of Perl by running the command:
[root@unixcop ~]# perl -v
This is perl 5, version 26, subversion 3 (v5.26.3) built for x86_64-linux-thread-multi
(with 55 registered patches, see perl -V for more detail)
Copyright 1987-2018, Larry Wall
Perl may be copied only under the terms of either the Artistic License or the
GNU General Public License, which may be found in the Perl 5 source kit.
Complete documentation for Perl, including FAQ lists, should be found on
this system using "man perl" or "perldoc perl". If you have access to the
Internet, point your browser at http://www.perl.org/, the Perl Home Page.
[root@unixcop ~]# Now you can download CSF using the curl command
[root@unixcop ~]# curl -O https://download.configserver.com/csf.tgz
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 2244k 100 2244k 0 0 655k 0 0:00:03 0:00:03 --:--:-- 655k
[root@unixcop ~]# As you can notice, it is quite lightweight. Now unzip it.
tar xvfz csf.tgzSo Access the folder generated, and inside it, run the installation script called install.sh
cd csf
sudo sh install.sh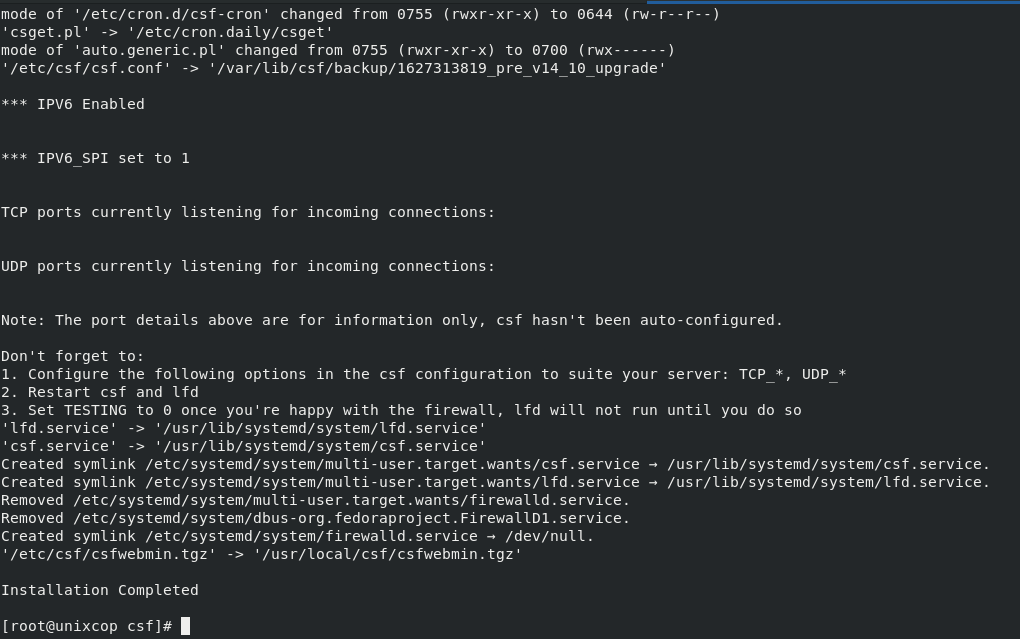
This will start the installation process and the default configuration will be applied.
Configuring CSF on CentOS 8
When installed, CFS applies some very good default settings, however, each of us has some fine-tuning to do.
The file is /etc/csf/csf.conf which should be backed up before editing to be sure.
sudo vim /etc/csf/csf.conf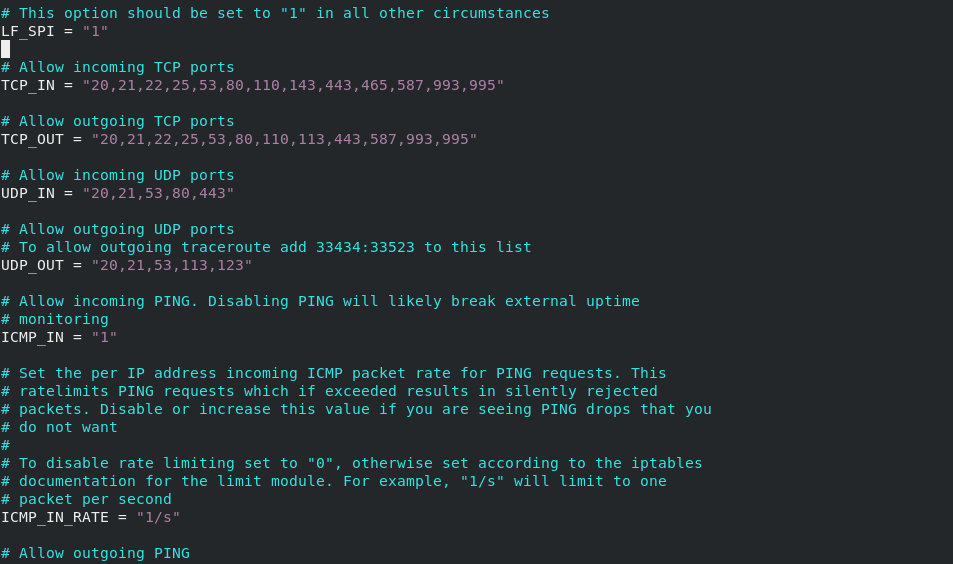
And in this file, you will find a lot of very well-documented parameters. And one of the most important sections is the one that lists the open ports for incoming and outgoing connections.
In this same file you can enable or disable CSF by changing the following value:
TESTING = "1"For
TESTING = "0"This way you indicate to the program that it is ready to start.
Save the changes and close the file.
Now you can start the CSF service.
sudo systemctl enable --now csfIt is also advisable to check the status of the service to see if it is running properly.
[root@unixcop csf]# sudo systemctl enable --now csf
[root@unixcop csf]# sudo systemctl status csf
● csf.service - ConfigServer Firewall & Security - csf
Loaded: loaded (/usr/lib/systemd/system/csf.service; enabled; vendor preset: disabled)
Active: active (exited) since Mon 2021-07-26 17:43:04 EET; 17s ago
Process: 20176 ExecStart=/usr/sbin/csf --initup (code=exited, status=0/SUCCESS)
Main PID: 20176 (code=exited, status=0/SUCCESS)
Jul 26 17:43:03 unixcop csf[20176]: ACCEPT all opt in * out lo ::/0 -> ::/0
Jul 26 17:43:03 unixcop csf[20176]: LOGDROPOUT all opt in * out !lo ::/0 -> ::/0
Jul 26 17:43:03 unixcop csf[20176]: LOGDROPIN all opt in !lo out * ::/0 -> ::/0
Jul 26 17:43:03 unixcop csf[20176]: csf: FASTSTART loading DNS (IPv4)
Jul 26 17:43:03 unixcop csf[20176]: csf: FASTSTART loading DNS (IPv6)
Jul 26 17:43:03 unixcop csf[20176]: LOCALOUTPUT all opt -- in * out !lo 0.0.0.0/0 -> 0.0.0.0/0
Jul 26 17:43:03 unixcop csf[20176]: LOCALINPUT all opt -- in !lo out * 0.0.0.0/0 -> 0.0.0.0/0
Jul 26 17:43:03 unixcop csf[20176]: LOCALOUTPUT all opt in * out !lo ::/0 -> ::/0
Jul 26 17:43:03 unixcop csf[20176]: LOCALINPUT all opt in !lo out * ::/0 -> ::/0
Jul 26 17:43:04 unixcop systemd[1]: Started ConfigServer Firewall & Security - csf.
[root@unixcop csf]# You can also check the ports that are open when CSF is running.
[root@unixcop csf]# sudo csf -p
Ports listening for external connections and the executables running behind them:
Port/Proto Open Conn PID/User Command Line Executable
22/tcp 4/6 1 (910/root) /usr/sbin/sshd -D -oCiphers=aes256-g... /usr/sbin/sshd
323/udp -/- - (853/chrony) /usr/sbin/chronyd /usr/sbin/chronyd
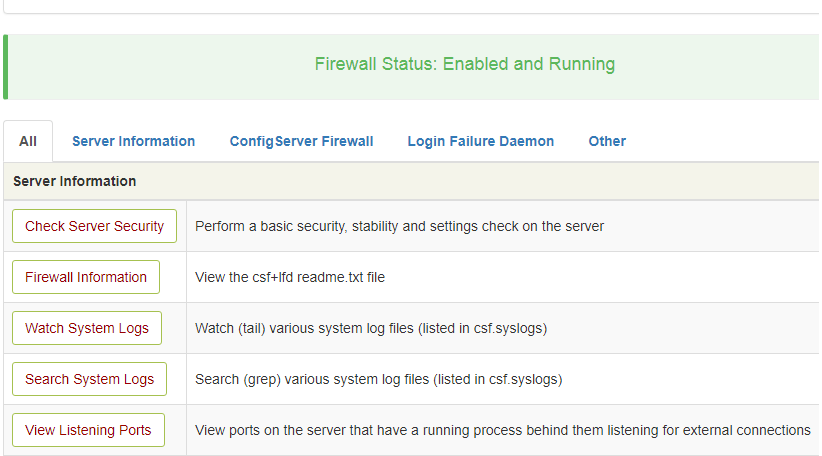
[root@unixcop csf]# Enable UI in CSF Firewall on CentOS
CSF Firewall come with standalone UI. This is disabled by default. On CentOS, install following requirments yum install perl-IO-Socket-SSL perl-Net-SSLeay perl-Net-LibIDN perl-IO-Socket-INET6 perl-Socket6
yum install perl-IO-Socket-SSL perl-Net-SSLeay perl-Net-LibIDN perl-IO-Socket-INET6 perl-SocketEdit CSF configuration file
vim /etc/csf/csf.confReplace UI = “0” with UI = “1”
Change following settins as needed.
UI_PORT = "6666"
UI_USER = "username"
UI_PASS = "password"By Default, only whitelisted IP can access the UI, to white list your IP, run
echo "YOUR_IP_ADDR" >> /etc/csf/ui/ui.allowIf you want to allow CSF UI from all IP address, then set UI_ALLOW to 0 in csf.conf
UI_ALLOW = "0"CSF use a self signed SSL, if you have an SSL cert, you can use it. SSL certificate is avaiable in folder
/etc/csf/ui/To use LetsEncrypt Free SSL certificate for CSF UI, i set symlink to ssl cert.
cd /etc/csf/ui
mv server.key server.key.old
mv server.crt server.crt.old
ln -s /etc/letsencrypt/live/DOMAIN/fullchain.pem server.crt
ln -s /etc/letsencrypt/live/DOMAIN/privkey.pem server.keyNow restart CSF and LDF
systemctl restart lfd
systemctl restart csfThis will prompt for user authentication first. After successful login, you will find the screen like below.
Conclusion
So you have learned how to install Config Server Firewall on CentOS 8 As you can notice the process is not complex but it does require some extra steps to complete the process.



