This post is about YARA Integration with WAZUH
Introduction
Wazuh can integrate with YARA in different ways. YARA is a versatile Open Source pattern-matching tool aimed to detect malware samples based on rule descriptions, although it is not limited to that use case alone.
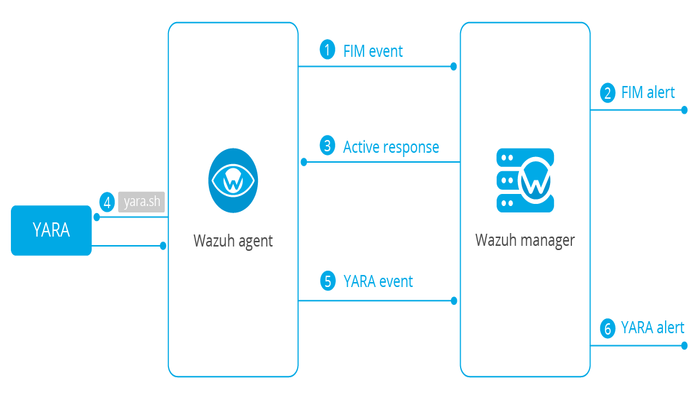
This use case focuses on automatically executing YARA scans by using the active response module when a Wazuh FIM alert is triggered. This is an interesting way of using YARA as it concentrates the scans on new or recently modified files in your environment, thus optimizing resource consumption on the monitored endpoints.
The next diagram illustrates the flow of events between the different components:
YARA Integration with WAZUH
The following section assumes Wazuh Manager is already installed . If you need to install it, you can do it following the WAZUH The Open Source Security Platform guide
First, configure the manager the action that you want to execute and under which circumstances you want it to be triggered. For that, edit the configuration file located at /var/ossec/etc/ossec.conf and add the following:
<ossec_config>
<command>
<name>yara</name>
<executable>yara.sh</executable>
<extra_args>-yara_path /path/to/yara -yara_rules /path/to/rules</extra_args>
<timeout_allowed>no</timeout_allowed>
</command>
<active-response>
<command>yara</command>
<location>local</location>
<rules_id>550,554</rules_id>
</active-response>
</ossec_config>Command
It contains information about the action to be executed on the agent, including its parameters:
- The
namesetting uniquely identifies the command,yara. - The script in the
executablesetting,yara.sh. - The
extra_argssetting needed to specify where the YARA binary and rules are located. - The
timeout_allowedsetting set to no. This represents a stateless active response.
Active response
It defines the criteria used to execute a specific command:
- The
commandto execute. It references theyaracommand created above. - The
locationsetting aslocal. It means that the active response is executed on the agent that generates the alert. - You can write a list of rule IDs that will trigger the active response in the
rules_idsetting. This example uses the following rule IDs.- Rule
550: file modified in the system - Rule
554: new file added to the system
- Rule
Rules and decoders
Define a set of rules and decoders to trigger alerts from the events generated by the YARA active response.
Create a decoder file, for example, /var/ossec/etc/decoders/yara_decoders.xml, and add the following:
<!--
- YARA decoders
- Created by Wazuh, Inc.
- Copyright (C) 2015-2022, Wazuh Inc.
- This program is a free software; you can redistribute it and/or modify it under the terms of GPLv2.
-->
<decoder name="yara">
<prematch>wazuh-yara: </prematch>
</decoder>
<decoder name="yara">
<parent>yara</parent>
<regex>wazuh-yara: (\S+) - Scan result: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara">
<parent>yara</parent>
<regex>wazuh-yara: (\S+) - Yara active response error. (\.+)</regex>
<order>log_type, error_message</order>
</decoder>Similarly create a rule file, /var/ossec/etc/rules/yara_rules.xml, with the following content:
<!--
- YARA rules
- Created by Wazuh, Inc.
- Copyright (C) 2015-2022, Wazuh Inc.
- This program is a free software; you can redistribute it and/or modify it under the terms of GPLv2.
-->
<group name="yara,">
<rule id="100100" level="0">
<decoded_as>yara</decoded_as>
<description>YARA rules grouped.</description>
</rule>
<rule id="100101" level="5">
<if_sid>100100</if_sid>
<field name="error_message">\.+</field>
<description>YARA error detected.</description>
</rule>
<rule id="100102" level="10">
<if_sid>100100</if_sid>
<field name="yara_rule">\.+</field>
<description>YARA $(yara_rule) detected.</description>
</rule>
</group>Restart the Wazuh manager for the changes to take effect.
Wazuh agent configuration
The following section assumes YARA is already installed on the monitored endpoint. If you need to install it, you can do it following the official YARA installation guide.
The script configured to run as part of the active response settings defined on the Wazuh manager, yara.sh, needs to be placed under /var/ossec/active-response/bin on the Wazuh agent side. Add the following content to it:
#!/bin/bash
# Wazuh - Yara active response
# Copyright (C) 2015-2022, Wazuh Inc.
#
# This program is free software; you can redistribute it
# and/or modify it under the terms of the GNU General Public
# License (version 2) as published by the FSF - Free Software
# Foundation.
#------------------------- Gather parameters -------------------------#
# Static active response parameters
LOCAL=`dirname $0`
# Extra arguments
read -r INPUT_JSON
YARA_PATH=$(echo $INPUT_JSON | jq -r .parameters.extra_args[1])
YARA_RULES=$(echo $INPUT_JSON | jq -r .parameters.extra_args[3])
FILENAME=$(echo $INPUT_JSON | jq -r .parameters.alert.syscheck.path)
COMMAND=$(echo $INPUT_JSON | jq -r .command)
# Move to the active response folder
cd $LOCAL
cd ../
# Set LOG_FILE path
PWD=`pwd`
LOG_FILE="${PWD}/../logs/active-responses.log"
#----------------------- Analyze parameters -----------------------#
if [[ ! $YARA_PATH ]] || [[ ! $YARA_RULES ]]
then
echo "wazuh-yara: ERROR - Yara active response error. Yara path and rules parameters are mandatory." >> ${LOG_FILE}
exit
fi
#------------------------ Analyze command -------------------------#
if [ ${COMMAND} = "add" ]
then
# Send control message to execd
printf '{"version":1,"origin":{"name":"yara","module":"active-response"},"command":"check_keys", "parameters":{"keys":[]}}\n'
read RESPONSE
COMMAND2=$(echo $RESPONSE | jq -r .command)
if [ ${COMMAND2} != "continue" ]
then
echo "wazuh-yara: INFO - Yara active response aborted." >> ${LOG_FILE}
exit 1;
fi
fi
#------------------------- Main workflow --------------------------#
# Execute Yara scan on the specified filename
yara_output="$("${YARA_PATH}"/yara -w -r "$YARA_RULES" "$FILENAME")"
if [[ $yara_output != "" ]]
then
# Iterate every detected rule and append it to the LOG_FILE
while read -r line; do
echo "wazuh-yara: INFO - Scan result: $line" >> ${LOG_FILE}
done <<< "$yara_output"
fi
exit 1;The script receives these paths:
- The file path contained in the alert that triggered the active response in the
parameters.alert.syscheck.pathobject. -yara_path. Path to the folder where the Yara executable is located; by default this is usually/usr/local/bin.-yara_rules. File path to the Yara rules file used for the scan.
The script uses the parameters above to perform a YARA scan:
# Execute YARA scan on the specified filename
yara_output="$("${YARA_PATH}"/yara -w -r "$YARA_RULES" "$FILENAME")"Then it analyzes the output to determine if the scan triggered any YARA rule:
# Iterate every detected rule and append it to the LOG_FILE
while read -r line; do
echo "wazuh-yara: INFO - Scan result: $line" >> ${LOG_FILE}
done <<< "$yara_output"For every line in the output, the script appends an event to the active response log, /var/ossec/logs/active-responses.log, with the following format:
wazuh-yara: INFO - Scan result: yara_rule file_pathMalware detection
Malware detection
HiddenWasp is a sophisticated malware that infects Linux systems, used for targeted remote control. Its authors took advantage of various publicly available Open Source malware, such as Mirai and Azazel rootkit.
It has three different components:
Deployment script. Initial attack vector.Rootkit. Artifact hiding mechanisms and TCP connection hiding.Trojan. C&C requests.
Deployment script
It is typically a bash script that tries to download the malware itself by connecting to an SFTP server. This script even updates the malware if the host was already compromised.
The main IoCs to look for in this component are the IP addresses and files that it copies to the system:
rule HiddenWasp_Deployment
{
strings:
$a = "http://103.206.123.13:8080/configUpdate.tar.gz"
$b = "http://103.206.123.13:8080/configUpdate-32.tar.gz"
$c = "http://103.206.123.13:8080/system.tar.gz"
$d = "103.206.123.13"
condition:
any of them
}Rootkit
User-space-based rootkit enforced via the LD_PRELOAD Linux mechanism and delivered as an ET_DYN stripped ELF binary. It tries to hide the trojan part of the malware by cloaking artifacts and TCP connections.
The following YARA rule detects its signature by using hexadecimal strings:
rule HiddenWasp_Rootkit
{
strings:
$a1 = { FF D? 89 ?? ?? 83 ?? ?? ?? 0F 84 [0-128] BF ?? ?? ?? ?? E8 ?? ?? ?? ?? 48 ?? ?? 48 ?? ?? ?? ?? ?? ?? 48 ?? ?? ?? ?? ?? ?? B8 ?? ?? ?? ?? FF D? 48 ?? ?? ?? 48 ?? ?? ?? ?? 74 [0-128] C6 ?? ?? ?? ?? ?? ?? BF ?? ?? ?? ?? E8 ?? ?? ?? ?? 48 ?? ?? ?? ?? ?? ?? 48 ?? ?? ?? ?? ?? ?? 48 ?? ?? BE ?? ?? ?? ?? }
$a2 = { 0F 84 [0-128] BF ?? ?? ?? ?? E8 ?? ?? ?? ?? 48 ?? ?? 48 ?? ?? ?? ?? ?? ?? 48 ?? ?? ?? ?? ?? ?? B8 ?? ?? ?? ?? FF D? }
$a3 = { 0F B6 ?? 83 ?? ?? 88 ?? 83 [0-128] 8B ?? ?? 3B ?? ?? 0F 82 [0-128] 48 ?? ?? ?? 48 }
$a4 = { 74 [0-128] C6 ?? ?? ?? ?? ?? ?? BF ?? ?? ?? ?? E8 ?? ?? ?? ?? 48 ?? ?? ?? ?? ?? ?? 48 ?? ?? ?? ?? ?? ?? 48 ?? ?? BE ?? ?? ?? ?? B8 ?? ?? ?? ?? E8 ?? ?? ?? ?? BF ?? ?? ?? ?? E8 ?? ?? ?? ?? 48 ?? ?? 48 ?? ?? ?? ?? ?? ?? 48 ?? ?? ?? ?? ?? ?? BF ?? ?? ?? ?? B8 ?? ?? ?? ?? FF D? 89 ?? ?? 83 ?? ?? ?? 0F 84 [0-128] BF ?? ?? ?? ?? E8 ?? ?? ?? ?? 48 ?? ?? 48 ?? ?? ?? ?? ?? ?? 48 ?? ?? ?? ?? ?? ?? B8 ?? ?? ?? ?? FF D? }
$b0 = { E8 ?? ?? ?? ?? 83 ?? ?? 83 ?? ?? FF B? ?? ?? ?? ?? E8 ?? ?? ?? ?? 83 [0-128] C6 ?? ?? ?? ?? ?? ?? FF 7? ?? 83 ?? ?? 6A ?? E8 ?? ?? ?? ?? 83 ?? ?? 5? 68 ?? ?? ?? ?? 8D ?? ?? ?? ?? ?? 5? E8 ?? ?? ?? ?? 83 ?? ?? 83 ?? ?? 83 ?? ?? 6A ?? E8 ?? ?? ?? ?? 83 ?? ?? 89 ?? 8D ?? ?? 5? 8D ?? ?? ?? ?? ?? 5? 6A ?? FF D? 83 ?? ?? 89 ?? ?? 83 ?? ?? ?? 0F 84 [0-128] 83 ?? ?? 83 ?? ?? 6A ?? E8 ?? ?? ?? ?? 83 ?? ?? 8D ?? ?? ?? ?? ?? 5? 8D ?? ?? ?? ?? ?? 5? FF D? 83}
$b1 = { 83 ?? ?? 83 ?? ?? 6A ?? E8 ?? ?? ?? ?? 83 ?? ?? 89 ?? 8D ?? ?? 5? FF 7? ?? 6A ?? FF D? 83 ?? ?? 89 ?? ?? 83 ?? ?? ?? 0F 84 [0-128] 83 ?? ?? 68 ?? ?? ?? ?? E8 ?? ?? ?? ?? 83 ?? ?? 89 ?? ?? ?? ?? ?? C6 ?? ?? ?? ?? ?? ?? FF 7? ?? 83 ?? ?? 6A ?? E8 ?? ?? ?? ?? 83 ?? ?? 5? 68 ?? ?? ?? ?? 8D ?? ?? ?? ?? ?? 5? E8 ?? ?? ?? ?? 83 ?? ?? 83 ?? ?? 83 ?? ?? 6A ?? E8 ?? ?? ?? ?? 83 ?? ?? 89 ?? 8D ?? ?? 5? }
$b2 = { 8B ?? ?? 8B ?? ?? 29 ?? 89 ?? 8B ?? ?? F7 ?? 21 ?? 23 ?? ?? 85 ?? 74 [0-128] 8B ?? ?? 83 ?? ?? 89 ?? ?? 8B ?? ?? 80 3? ?? 75 [0-128] 8B ?? ?? 8B ?? ?? 29}
$b3 = { 8B ?? ?? 29 ?? 89 ?? 8B ?? ?? F7 ?? 21 ?? 23 ?? ?? 85 ?? 74 [0-128] 8B ?? ?? 83 ?? ?? 89 ?? ?? 8B ?? ?? 80 3? ?? 75 [0-128] 8B}
$b4 = { 83 ?? ?? 8B ?? ?? 89 ?? ?? 8B ?? ?? 89 [0-128] 8B ?? ?? 89 ?? 8D ?? ?? FF 0? 8A ?? 88 ?? ?? 8B ?? ?? 89 ?? 8D ?? ?? FF 0? 8A ?? 88 ?? ?? 80 7? ?? ?? 75 [0-128] 8A ?? ??}
condition:
all of ($a*) or all of ($b*)
}Wazuh alerts
The YARA rules above generate these alerts when executed through the Wazuh active response
{
"timestamp": "2020-06-09T08:15:07.187+0000",
"rule": {
"level": 10,
"description": "YARA HiddenWasp_Deployment detected.",
"id": "100102",
"firedtimes": 1,
"mail": false,
"groups": ["yara"]
},
"agent": {
"id": "001",
"name": "yara-agent",
"ip": "10.0.2.x"
},
"manager": {
"name": "wazuh-manager"
},
"id": "1591690507.38027",
"full_log": "wazuh-yara: info: HiddenWasp_Deployment /home/user/script.sh",
"decoder": {
"name": "yara"
},
"data": {
"yara_rule": "HiddenWasp_Deployment",
"file_path": "/home/user/script.sh"
},
"location": "/var/ossec/logs/active-responses.log"
}{
"timestamp": "2020-06-09T08:18:47.901+0000",
"rule": {
"level": 10,
"description": "YARA HiddenWasp_Rootkit detected.",
"id": "100102",
"firedtimes": 1,
"mail": false,
"groups": ["yara"]
},
"agent": {
"id": "001",
"name": "yara-agent",
"ip": "10.0.2.x"
},
"manager": {
"name": "wazuh-manager"
},
"id": "1591690407.33120",
"full_log": "wazuh-yara: info: HiddenWasp_Rootkit /home/user/binary",
"decoder": {
"name": "yara"
},
"data": {
"yara_rule": "HiddenWasp_Rootkit",
"file_path": "/home/user/binary"
},
"location": "/var/ossec/logs/active-responses.log"
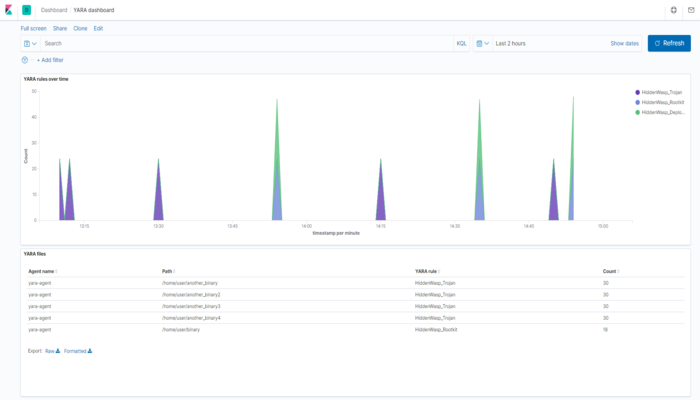
}You can also create custom dashboards in Kibana for this integration: